SealPath Cyber Security & Enterprise Data Protection — Worldwide
Zero-Trust EDRM — Your Data Stays Protected Wherever It Travels, Across Every Border
SealPath is the world's leading Enterprise Digital Rights Management (EDRM) platform trusted by banks, law firms, hospitals, and manufacturers across six continents. As an Authorized Global Reseller of SealPath, TekkPak Technologies delivers military-grade encryption, dynamic access control, and real-time document tracking to give your business persistent, borderless data protection — no matter where your teams, partners, or clients are located.
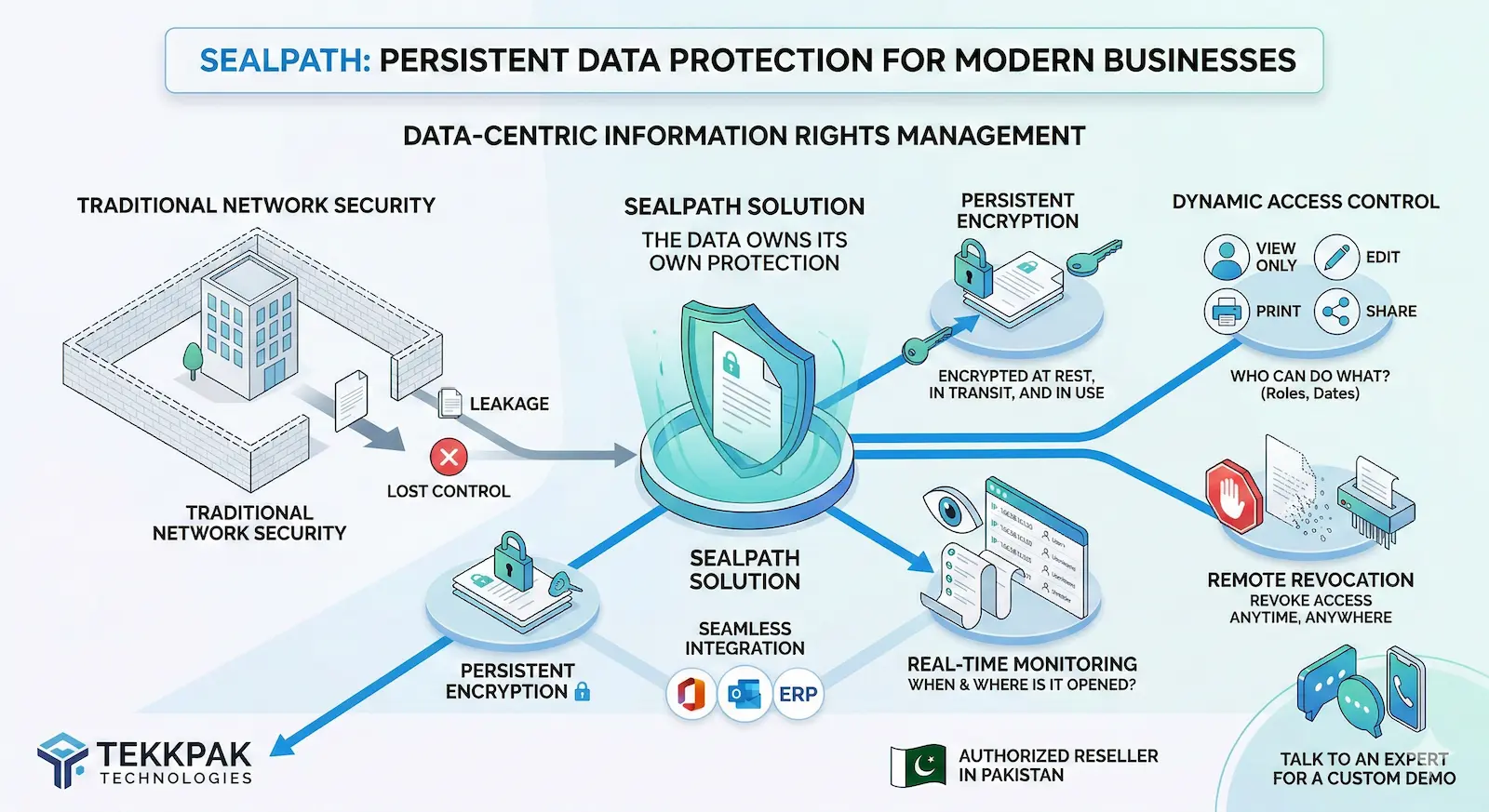
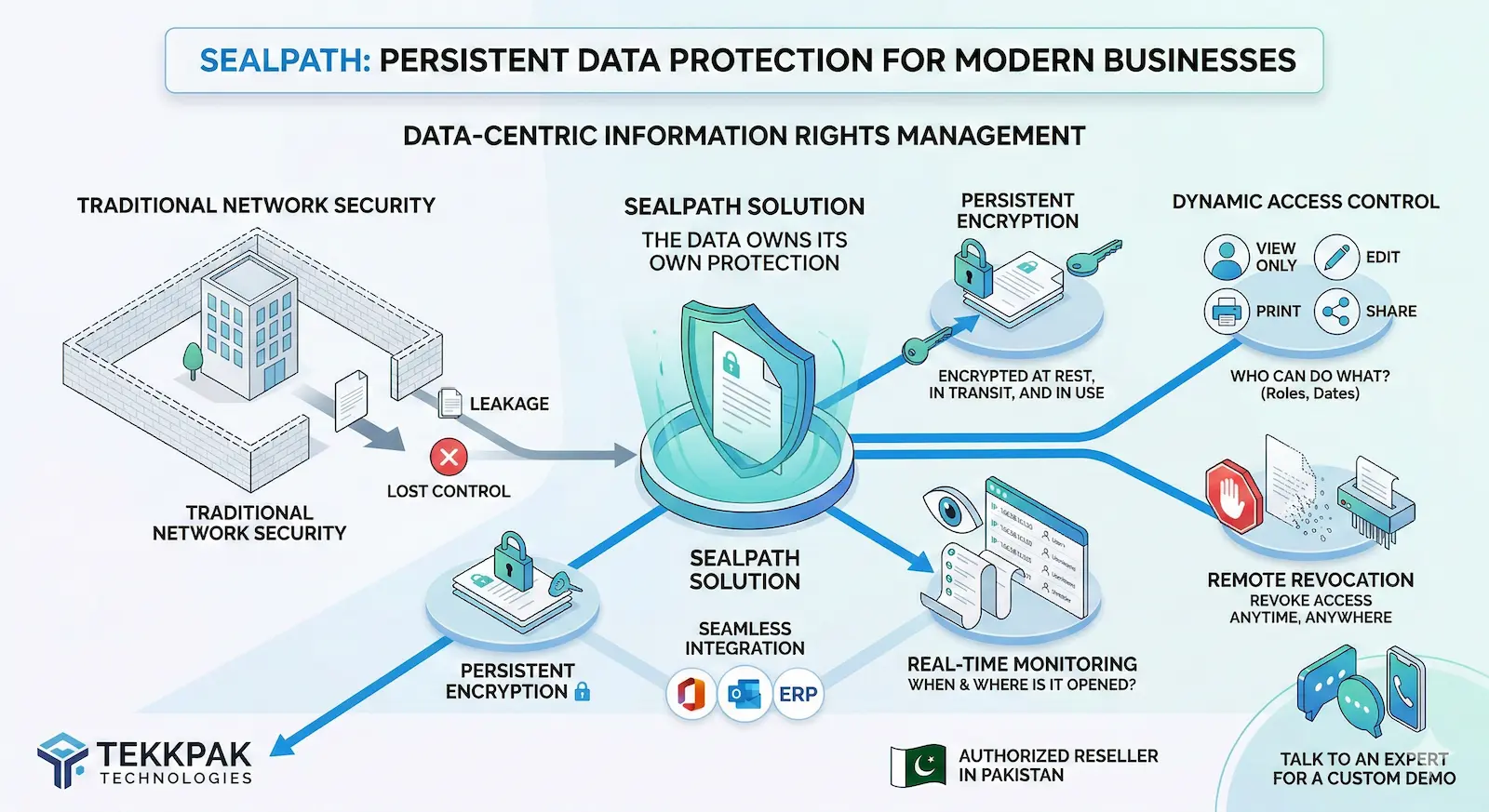
Understanding the Technology
What is SealPath? The Future of Data-Centric Security
SealPath is a pioneering Information Rights Management (IRM) and Enterprise Digital Rights Management (EDRM) platform developed in Spain and deployed globally across Fortune 500 enterprises, government agencies, and SMEs.
Unlike traditional cybersecurity tools — firewalls, antivirus, DLP — that guard the perimeter of your network, SealPath protects the document itself. Encryption and access policies travel inside the file, making the document its own security perimeter. Whether it lands on a USB drive, in a Gmail inbox, or in a foreign data center, only authorized users can ever open it.
This approach is called Zero-Trust Data Security and it is fast becoming the global gold standard as remote work, cloud collaboration, and sophisticated insider threats make perimeter-based security obsolete.
- Protection persists outside your corporate network — always
- Users authenticate identity before opening any protected file
- Granular permissions: View, Edit, Print, Copy — you decide
- Automatic document expiry and remote one-click revocation
- Full audit trail with open/fail logs, timestamps, and IP addresses
- Native integration with Microsoft 365, SharePoint, and leading ERPs
Core SealPath Features
Every feature of SealPath is engineered around one principle: your data remains under your control, always — no matter where it goes.
Persistent AES-256 Encryption
SealPath encrypts files at rest, in transit, and in active use simultaneously. The encryption is persistent — it travels inside the document and cannot be removed by anyone except the owner. Even if a file is copied to a USB, shared via WhatsApp, or uploaded to personal cloud storage, the data remains fully encrypted and inaccessible to unauthorized parties.
Granular Dynamic Access Control
Define precisely what each recipient can do with your document. Grant View-Only access, allow editing, permit printing, or block copy-pasting entirely — per user or per group. Set automatic expiration dates so that project files become unreadable on a specific date with zero manual intervention, ensuring time-limited vendor or contractor access.
Real-Time Document Auditing
SealPath's audit dashboard gives you a comprehensive, real-time log of every interaction with your protected documents. Know exactly who opened your file, when, from which device, and from which geographic IP location. Receive instant alerts when an unauthorized user attempts — and fails — to access sensitive data, giving your security team actionable intelligence.
Instant Remote Revocation
Mistakes happen. Employees resign. Contracts end. With SealPath, you can revoke access to any document with a single click from the admin console — instantly. Even if the file is already downloaded on a device in another country, it becomes permanently unreadable the moment you hit revoke. No need to chase down files or reset passwords.
Seamless Microsoft 365 Integration
SealPath integrates natively with Microsoft Word, Excel, PowerPoint, Outlook, SharePoint, OneDrive, and Active Directory. Authorized users protect and open files directly from within familiar applications with no additional training required. It also integrates with AutoCAD, leading ERPs like SAP and Odoo, and classification tools like Microsoft Purview (formerly AIP).
Automated Policy-Based Folder Protection
Define security policies and apply them to entire network folders or SharePoint libraries. Any file dropped into a SealPath-protected folder automatically inherits your organization's predefined access rules — with zero user effort. This enables mass-protection of existing document repositories without requiring employees to manually apply policies file by file.
How SealPath Works — 4 Simple Steps
SealPath's Zero-Trust protection model is powerful yet invisible to legitimate users. Here's how your documents stay safe from creation to consumption.
Create & Classify
Your employee creates a document in Word, Excel, or AutoCAD. SealPath automatically classifies it based on content sensitivity labels (Confidential, Internal, Public) aligned with your policy.
Protect & Encrypt
The document is encrypted with AES-256. A rights policy is embedded — specifying exactly who can open, edit, print, or share it, and for how long. The file is now its own security boundary.
Share Freely & Securely
Send the file via email, WhatsApp, USB, cloud, or FTP. The protection travels with it. Recipients see a normal-looking file. When they try to open it, SealPath silently verifies their identity and rights.
Monitor, Revoke & Control
Watch your audit dashboard for real-time open logs and access attempts. Modify permissions or revoke access at any time — changes take effect instantly across all locations and devices.
SealPath Across Industries — Worldwide
SealPath is industry-agnostic and geography-agnostic. Wherever sensitive documents are created, shared, or stored, SealPath eliminates the risk. Here are the key verticals we serve globally.
Banking & Financial Services
Banks, investment firms, and financial institutions worldwide handle PCI-DSS regulated cardholder data, board reports, and confidential loan portfolios. SealPath ensures that financial documents shared with auditors, regulators, or board members can never be forwarded, printed, or screenshotted without permission — helping you meet the strictest financial sector cybersecurity mandates globally.
Manufacturing & Engineering
Your CAD drawings, product blueprints, and proprietary formulas are your competitive moat. When you share designs with outsourced vendors or factories, SealPath grants time-limited View-Only access that expires automatically on contract end — preventing intellectual property theft that costs manufacturers billions annually, regardless of which country or continent your partners operate in.
Healthcare & Pharmaceuticals
Patient records, clinical trial data, and pharmaceutical R&D must be shared between clinics, labs, and insurers — but never leaked. SealPath encrypts electronic health records (EHRs) and provides a full audit trail of every access, supporting HIPAA, GDPR, and regional data protection requirements for healthcare organizations worldwide.
Legal, M&A & Consulting
Law firms, investment banks, and management consultants routinely share highly sensitive M&A documents, litigation files, and due diligence reports. SealPath creates a secure virtual data room experience inside normal files — with document expiration, view-only access, and comprehensive access logs that protect attorney-client privilege.
Construction & Real Estate
Architectural plans, land agreements, and developer contracts involve multiple third-party stakeholders. SealPath protects project documents shared with contractors, architects, and investors, ensuring plans cannot be copied or leaked to competitors during the bidding and approval phase.
Education & Research Institutions
Universities and research bodies generate valuable IP in the form of research papers, grant proposals, and examination materials. SealPath protects academic intellectual property during peer review and collaboration, preventing premature disclosure or unauthorized reproduction of proprietary research findings.
Government & Public Sector
Ministries and government agencies handle classified policy documents, procurement files, and inter-departmental communications. SealPath enforces national-grade document classification and access control aligned with government cybersecurity frameworks, protecting sensitive state information from unauthorized disclosure.
Supply Chain & Logistics
Import-export businesses, freight forwarders, and logistics companies exchange hundreds of sensitive customs documents, contracts, and pricing sheets daily. SealPath ensures these documents can only be accessed by designated supply chain partners and automatically expire at shipment completion, eliminating commercial espionage risk.
The SealPath Difference: Real Scenarios Before & After
Traditional security leaves massive gaps. SealPath closes every one of them. See exactly how document security transforms in the real world.
| Real-World Scenario | ❌ Without SealPath | ✅ With SealPath |
|---|---|---|
| File Emailed to Wrong Recipient | Recipient opens the file immediately. A data breach is confirmed. Reputational and legal damage follows. | Recipient cannot open the file. SealPath alerts you of the failed access attempt. No breach occurs. |
| Employee Resignation | Ex-employee walks out with client lists, contracts, and IP on a USB drive. No way to recover or delete the data remotely. | IT revokes access in seconds. All downloaded files instantly become permanently unreadable on every device. |
| Document Shared with Vendor | Vendor shares the file with a competitor. Your IP is now in the hands of the market. | Vendor access is View-Only with no forwarding rights. Document expires at contract end. IP stays yours. |
| File Uploaded to Personal Cloud | Once on Google Drive or Dropbox, corporate security tools lose all jurisdiction over the file. | SealPath protection travels with the file. It is still encrypted and requires authentication on any cloud platform. |
| Regulatory Audit or Compliance Check | No audit trail. Unable to prove document security controls to regulators. Heavy fines and compliance failures. | Complete audit log: who accessed what, when, from where. Instant compliance reporting for SBP, SECP, HIPAA, GDPR. |
| Remote / Work-From-Home Employee | Files downloaded on home PCs that lack corporate security controls. Data is exposed on personal devices. | SealPath verifies the user's identity and device context before allowing any access. Security follows the employee. |
SealPath vs. Traditional DLP Solutions
Traditional Data Loss Prevention (DLP) tools block file transfers. SealPath takes a fundamentally different — and more effective — approach.
❌ Traditional DLP & Perimeter Tools
✅ SealPath Cyber Security (EDRM)
SealPath Supports Global & Pakistan Compliance Standards
Regulatory compliance is no longer optional. SealPath's persistent encryption and audit capabilities directly support the most demanding international and local data protection frameworks.
Financial Sector Regulations
SealPath satisfies data protection and cybersecurity directives issued by financial regulators worldwide — including the FCA, SEC, FINRA, SBP, and equivalent national banking authorities — covering encryption and access control mandates.
GDPR (EU Data Protection)
SealPath's persistent encryption and audit log capabilities directly support GDPR Articles 25, 32, and 33 — covering data protection by design, breach notification, and security obligations.
HIPAA Healthcare Compliance
For healthcare providers sharing Protected Health Information (PHI), SealPath provides the encryption, access control, and audit trail required by HIPAA's Security Rule, minimizing breach liability.
PCI-DSS & ISO 27001
SealPath's AES-256 encryption and role-based access controls align with PCI-DSS requirements for cardholder data and ISO 27001 information security management system (ISMS) standards.
What Our Clients Say About SealPath in Pakistan
Before TekkPak deployed SealPath, we had no visibility into what happened to our board reports once they left our servers. Now we receive real-time alerts, our documents auto-expire, and we have full compliance reporting for our external auditors. It transformed our data governance posture overnight.
We manufacture precision engineering components and our CAD designs are our core IP. After a competitor replicated one of our products, we implemented SealPath with TekkPak's help. Now every blueprint shared with vendors is View-Only with an automatic 30-day expiry. IP theft has become technically impossible.
Our healthcare network spans 12 clinics sharing thousands of patient records monthly. HIPAA compliance felt unachievable until SealPath. Now every patient document is encrypted end-to-end and we have a complete, timestamped access log for every file. TekkPak's local support team made the entire deployment seamless.
Why Choose TekkPak Technologies as Your SealPath Partner?
As an Authorized SealPath Reseller serving clients globally, TekkPak brings deep technical expertise, responsive multilingual support, and a compliance-first deployment approach to every engagement — wherever your organization is based.
Authorized Reseller Status
TekkPak Technologies is an official, authorized reseller of SealPath — guaranteeing you access to genuine licenses, official product updates, and manufacturer-backed warranties with full legal standing, regardless of the country or region your organization operates in.
Remote & On-Site Global Deployment
Our team of certified cybersecurity engineers delivers SealPath deployments remotely or on-site — anywhere in the world. From Active Directory integration to policy configuration and end-user training, we manage the entire process with bilingual support across time zones.
Flexible Licensing & Multi-Currency Billing
TekkPak offers flexible per-user and enterprise volume licensing with monthly and annual billing options in multiple currencies — USD, EUR, GBP, PKR, and more. We make commercial procurement straightforward for clients across different regions and regulatory environments.
Enterprise ERP & Infrastructure Integration
Beyond SealPath, TekkPak is a specialist in end-to-end enterprise IT. We seamlessly integrate SealPath with your existing Odoo ERP, SAP, Microsoft 365 tenant, Grandstream IP telephony, or 3CX communications platform — creating a unified, secure digital infrastructure for your organization.
Compliance-First Approach
Our security consultants map SealPath policies to your specific regulatory obligations — whether that is GDPR, HIPAA, ISO 27001, PCI-DSS, NIS2, DORA, or sector-specific national frameworks — ensuring your deployment is audit-ready and regulator-facing from day one.
Training & Change Management
User adoption is the key to security ROI. TekkPak provides comprehensive employee training workshops, policy documentation, and ongoing change management support to ensure your team embraces SealPath confidently.
Frequently Asked Questions About SealPath
What exactly is SealPath and how does it differ from antivirus software?
SealPath is an Enterprise Digital Rights Management (EDRM) and Information Rights Management (IRM) platform. Unlike antivirus software which detects and removes malware, or firewalls which block network intrusions, SealPath protects the data itself using persistent encryption. The protection travels inside the document and remains active no matter where the file goes — on personal devices, external cloud storage, or foreign email servers. Antivirus cannot help once your file has been emailed to the wrong person; SealPath can.
Will SealPath slow down my employees or disrupt their workflow?
No — SealPath is specifically designed for transparent, frictionless user experience. Authorized users open protected files in Microsoft Word, Excel, PowerPoint, Outlook, or AutoCAD exactly as they normally would. SealPath performs identity verification silently in the background in milliseconds. There is no separate password, no special viewer required, and no change to daily workflows. Only unauthorized users experience the system — through a clean denial of access.
What happens if a SealPath-protected file is copied to a USB drive or shared via WhatsApp?
The file remains fully encrypted and protected regardless of how it is transferred. If anyone — authorized or not — tries to open the file from a USB drive, WhatsApp download, or any other medium, SealPath checks their identity and access rights in real time against the cloud policy server. Authorized users open the file normally. Unauthorized users cannot open it under any circumstances, and you receive an alert of the failed access attempt.
How quickly can SealPath be deployed across our organization?
A standard SealPath deployment for a mid-sized organization (50–500 users) typically takes between 3 to 10 business days from license activation to full go-live, depending on the complexity of Active Directory integration and the number of custom policy templates required. TekkPak's certified team handles the entire deployment remotely — across any time zone — or on-site at your premises, including policy design, AD sync, Microsoft 365 integration, and end-user training.
Does SealPath work if the recipient does not have the SealPath client installed?
Yes. SealPath offers a web-based viewer for recipients who do not have the desktop client installed. External users — such as clients, auditors, or partners — can be granted access via a secure web browser link. They authenticate with their business email and access the document within the SealPath secure online viewer with whatever permissions you have granted them (View-Only, Print, etc.) — without needing to download or install anything.
Is SealPath suitable for small and medium businesses (SMBs), or only for large enterprises?
SealPath is designed to scale from individual professionals and small teams up to multinational enterprise deployments. TekkPak offers flexible per-user licensing starting from as few as 5 users, making SealPath highly accessible and cost-effective for SMBs worldwide — in legal, accounting, consultancy, design, and trading sectors. The cloud-hosted SaaS deployment model means there is no server infrastructure to purchase or maintain, removing barriers to entry for organizations of any size and in any country.
Stop Losing Control of Your Data. Start with SealPath Today.
Every day without SealPath is a day your most sensitive documents are one email away from a catastrophic breach. Join organizations across six continents that trust TekkPak Technologies and SealPath to keep their data permanently protected — across every device, border, and cloud.
🌍 Serving enterprises globally — Remote deployment available worldwide · On-site support in select regions