Logsign Cybersecurity
SIEM & SOAR Platform
Pakistan's most trusted implementation partner for Logsign — the Unified Security Operations Platform delivering real-time threat detection and automated incident response for enterprises, banks, hospitals, and government institutions.
What Is Logsign?
Logsign is a next-generation Unified Security Operations Platform (USOP) that merges SIEM, SOAR, and Threat Intelligence into a single, cohesive environment. Designed to replace fragmented, legacy security stacks, Logsign empowers organizations to detect, investigate, and neutralize cyber threats — all from one powerful dashboard.
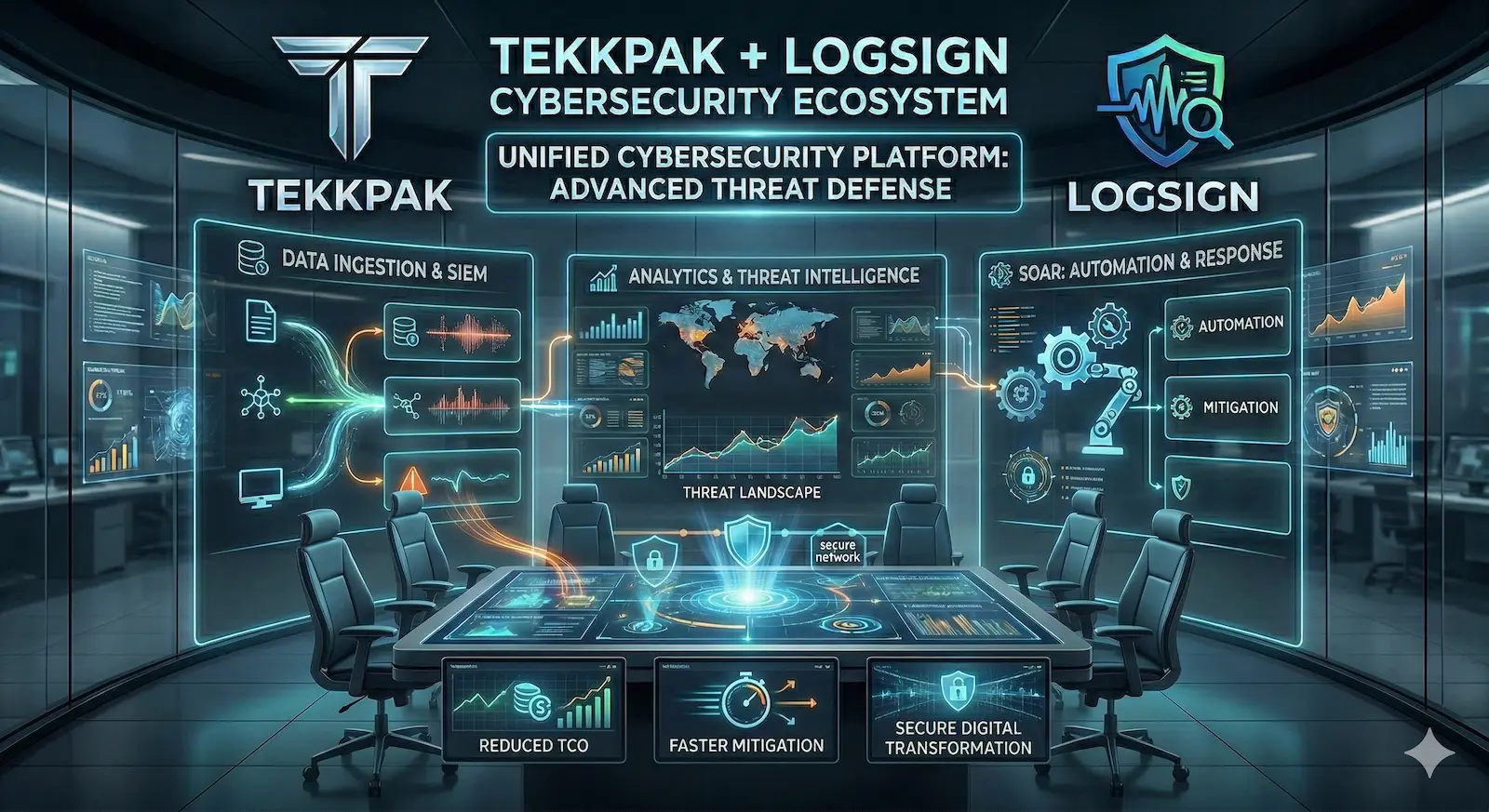
Logsign Platform Architecture
How data flows from your infrastructure into intelligence-driven action
Data Ingestion Layer
Firewalls, endpoints, cloud, apps, IoT & network devices stream logs at scale
→SIEM Intelligence Engine
AI-powered correlation, anomaly detection, and threat scoring across all data sources
→SOAR Automation Layer
Automated playbooks trigger instant containment, isolation, and remediation actions
Logsign Key Features
Every capability within the Logsign platform is engineered to reduce complexity, accelerate response, and give your security team the upper hand against modern threats.
Unified SIEM & SOAR
Logsign eliminates security silos by natively combining data aggregation, real-time correlation, threat intelligence, and automated playbook execution into a single, intuitive platform — no expensive bolt-on integrations required.
Real-Time Threat Intelligence
Proactively monitors billions of log events across your entire network fabric. Logsign's ML-driven correlation engine identifies sophisticated threats, insider attacks, and zero-day anomalies within milliseconds of occurrence.
Automated Incident Response
Reduce Mean Time to Respond (MTTR) from hours to seconds. Logsign's SOAR engine automatically quarantines compromised endpoints, resets credentials, blocks malicious IPs, and executes multi-step remediation without human intervention.
Limitless Scalability
Built on a distributed big-data architecture, Logsign ingests and processes massive log volumes without performance degradation. Scale from a 50-user SMB to a 50,000-node enterprise — the platform grows with you, not against you.
Compliance & Reporting
One-click compliance reports for ISO 27001, PCI-DSS, GDPR, HIPAA, NIST, SOC 2, and State Bank of Pakistan (SBP) Cybersecurity Framework. Logsign makes audit season effortless with fully customizable, export-ready reporting.
Intuitive Visual Interface
Logsign's drag-and-drop investigation dashboard eliminates steep learning curves. Security analysts at every skill level can build correlation rules, run investigations, and orchestrate automated playbooks without specialized programming knowledge.
Beyond Basic SIEM — Logsign's Extended Security Arsenal
Logsign goes far beyond traditional log management, delivering a comprehensive suite of advanced detection and response capabilities built for today's sophisticated threat landscape.
UEBA — User & Entity Behavior Analytics
Logsign's UEBA module builds behavioral baselines for every user, device, and application. Subtle deviations — such as unusual login times, abnormal data downloads, or lateral movement — are flagged automatically, catching insider threats and compromised accounts before damage occurs.
Threat Hunting & Investigation
Empower your SOC analysts with Logsign's powerful search engine. Conduct retrospective threat hunts across months of historical log data in seconds, pivot on IoCs (Indicators of Compromise), and reconstruct entire attack kill chains with visual timeline mapping.
Multi-Cloud & Hybrid Coverage
Logsign provides end-to-end visibility across on-premises, private cloud, AWS, Azure, and Google Cloud environments. A single pane of glass for your entire hybrid infrastructure — because attackers don't care about your network boundaries.
Automated Playbooks & Orchestration
Design sophisticated multi-step automation workflows using Logsign's visual playbook editor. Connect to firewalls, ticketing systems, email gateways, and endpoint solutions to execute complex response chains — all without writing a single line of code.
Threat Intelligence Integration
Logsign ingests global threat intelligence feeds (MISP, VirusTotal, AlienVault OTX, and more), automatically enriching every alert with real-world context. Know immediately if a detected IP is part of a known botnet or if a file hash is associated with ransomware.
Custom Dashboards & Alerts
Build fully tailored, role-based dashboards for CISOs, SOC analysts, compliance officers, and executives. Configure granular alerting thresholds, escalation workflows, and notification channels including email, SMS, Slack, and ITSM platforms.
Logsign Supports Pakistan & Global Compliance Mandates
Compliance reporting that used to take weeks now takes minutes. Logsign's pre-built compliance packs map log data directly to regulatory controls — keeping your organization audit-ready at all times.
Why Your Organization Needs Logsign Now
The cost of a single data breach far exceeds the investment in proactive security. Logsign delivers measurable, immediate ROI by transforming your security operations from reactive firefighting to proactive threat dominance.
Reduced Total Cost of Ownership
Replace 4–6 fragmented point solutions with one unified platform. Eliminate costly add-on modules, reduce licensing complexity, and slash operational overhead — without compromising coverage or capability.
Rapid Time-to-Value
TekkPak's certified engineers deploy and configure Logsign in your environment within days. Pre-built content packs, correlation rules, and dashboards mean your SOC is generating insights from day one — not month three.
Amplified Team Productivity
Automation handles the routine. By eliminating repetitive manual alert triage, your analysts focus on strategic threat hunting and high-impact investigations — doubling effective SOC output without adding headcount.
Zero-Day & Ransomware Defense
Stop advanced persistent threats, ransomware propagation, and business email compromise before exfiltration occurs. Logsign's behavioral analytics and automated containment shut down attacks mid-kill-chain.
False Positive Reduction
Drown in thousands of false-positive alerts no more. Logsign's ML-powered risk scoring and contextual enrichment filter noise with precision — your team acts only on verified, high-fidelity threats that demand attention.
Local Expertise, Global Standards
TekkPak's Pakistan-based engineers understand local compliance landscapes, infrastructure realities, and threat actors. You get world-class Logsign capabilities paired with on-the-ground support that multinational vendors simply cannot offer.
Logsign Deployment by TekkPak — A Proven 4-Step Process
Our structured implementation methodology ensures your Logsign SIEM & SOAR platform is deployed correctly, configured optimally, and generating security value from day one.
Discovery & Assessment
TekkPak engineers conduct a thorough audit of your existing infrastructure, security gaps, log sources, and compliance requirements to design the optimal Logsign architecture.
Platform Deployment
Logsign is deployed on-premises, in your private cloud, or as a hybrid configuration. All log sources — firewalls, endpoints, servers, cloud apps — are onboarded and normalized.
Configuration & Tuning
Correlation rules, detection use cases, automated playbooks, and compliance reports are customized to your specific threat model and regulatory obligations — including SBP and PCI-DSS requirements.
Training & Ongoing Support
Your team receives hands-on Logsign training. TekkPak provides ongoing managed support, platform updates, new use case development, and quarterly security reviews — keeping you protected as threats evolve.
Logsign Cybersecurity Across Every Industry in Pakistan
From Karachi's financial district to Islamabad's government corridors and Lahore's growing tech sector, Logsign adapts to the unique security requirements of every industry vertical.
Financial Institutions
Pakistan's banks, microfinance institutions, and fintech companies are prime targets for fraud, APTs, and regulatory penalties. Logsign provides real-time transaction anomaly monitoring, privileged access governance, and automated SBP compliance reporting. Detect account takeover attempts, ATM network breaches, and SWIFT transaction fraud before they escalate into critical incidents.
Healthcare Sector
Hospitals and health networks store irreplaceable patient records that attract ransomware operators worldwide. Logsign secures EHR systems, medical IoT devices, and telemedicine portals — ensuring patient data confidentiality, preventing care-disrupting ransomware attacks, and maintaining compliance with international health privacy frameworks. Logsign keeps your focus on patients, not incidents.
Retail & E-Commerce
Pakistan's booming e-commerce ecosystem faces DDoS attacks, payment gateway skimming, and supply-chain compromises daily. Logsign monitors web traffic, application logs, and payment infrastructure in real-time — auto-blocking malicious IPs, detecting card-skimming scripts, and securing the complete customer data lifecycle from browse to checkout.
Higher Education
Universities and research institutions manage sprawling, open networks accessed by thousands of users daily. Logsign protects academic research data, secures cloud-hosted learning platforms, detects unauthorized access to sensitive research databases, and ensures compliance with data protection obligations — without disrupting the open, collaborative academic environment.
Government & Defence
Critical national infrastructure, citizen data portals, and classified government systems demand the highest level of security monitoring. Logsign delivers classified-grade log analytics, insider threat detection, and full audit trails that meet national cybersecurity directives — supporting Pakistan's digital government transformation securely.
Telecom & ISPs
Telecommunications providers are high-value targets due to their access to vast subscriber data and national communication networks. Logsign monitors network operations centers, OSS/BSS systems, and subscriber data platforms — detecting SS7 exploits, CDR manipulation, and network intrusions while enabling PTA compliance and rapid incident response at carrier scale.
Logsign Integrates With Your Entire Security Stack
With 500+ out-of-the-box connectors, Logsign slots seamlessly into your existing infrastructure. No rip-and-replace — it enhances and unifies what you already have.
Before vs. After Logsign Deployment
The difference between a reactive and a proactive security posture is stark. See exactly how Logsign transforms your organization's security operations from day one.
| Security Domain | ❌ Before Logsign (Legacy Setup) | ✅ After Logsign by TekkPak |
|---|---|---|
| Threat Detection | Manual log reviews; breaches discovered days or weeks after compromise. MTTD measured in weeks. | AI-driven real-time anomaly detection. Threats identified and flagged within milliseconds. MTTD < 1 minute. |
| Incident Response | IT team manually disables accounts, blocks IPs, re-images systems — significant downtime and data loss risk. | Automated SOAR playbooks neutralize threats instantly. Compromised nodes quarantined, credentials reset, and tickets raised — automatically. |
| Alert Management | Thousands of raw, unfiltered, false-positive alerts daily. Analyst fatigue leads to missed critical events. | ML-powered risk scoring filters noise. Analysts receive only high-fidelity, contextually enriched alerts that require genuine action. |
| Compliance Reporting | Days of manual data compilation from fragmented sources. Audit preparation consumes entire teams. | One-click compliance reports mapped to SBP, ISO 27001, PCI-DSS, GDPR from a centralized dashboard. Audit-ready at all times. |
| Visibility | Fragmented tools provide isolated views. Blind spots across cloud, on-premises, and remote endpoints. | Single pane of glass across all environments — on-premises, cloud, hybrid, remote workforce, OT/IoT. |
| Operational Cost | Multiple overlapping tools with separate licensing, maintenance, and specialist staff requirements. | One unified platform replaces 4–6 point solutions. Dramatically lower TCO, reduced headcount requirements. |
Logsign vs. Legacy SIEM Competitors
When evaluated against established players like Splunk, IBM QRadar, and Microsoft Sentinel, Logsign consistently delivers superior value, faster deployment, and lower total cost — particularly for organizations in emerging markets like Pakistan.
| Evaluation Criterion | Logsign SIEM & SOAR | Splunk Enterprise Security | IBM QRadar |
|---|---|---|---|
| Unified SIEM + SOAR | ✔ Native — single platform | ✘ SOAR requires separate SOAR Premium license | ✘ SOAR via separate Resilient acquisition |
| Total Cost of Ownership | ✔ Transparent, predictable pricing | ✘ Prohibitive — scales aggressively with data volume | ✘ High entry cost + expensive professional services |
| Deployment Speed | ✔ Days with TekkPak's experts | ✘ Months of complex configuration | ✘ Months; requires specialized IBM-certified engineers |
| Ease of Use | ✔ Visual drag-and-drop; minimal training | ✘ Proprietary SPL query language; steep learning curve | ✘ Complex AQL; requires dedicated certified analysts |
| Local Pakistan Support | ✔ TekkPak — on-ground, Pakistan-based team | ✘ Remote international support; time-zone issues | ✘ Limited local presence in Pakistan |
| SME Suitability | ✔ Scalable from SMB to large enterprise | ✘ Enterprise-only; cost-prohibitive for mid-market | ✘ Enterprise-grade pricing; not SME-accessible |
What Our Clients Say About Logsign in Pakistan
Real outcomes from real organizations that trusted TekkPak Technologies to deploy and manage their Logsign Security Operations Platform.
"Before partnering with TekkPak Technologies, our IT team was drowning in thousands of false-positive security alerts daily. Deploying Logsign completely transformed our SOC. The automated SOAR capabilities reduced our incident response time by 90%, allowing us to secure our nationwide retail network effortlessly. The ROI was visible within the first quarter."
"As a regulated financial service provider, data security and SBP compliance are non-negotiable. TekkPak implemented Logsign SIEM flawlessly into our complex multi-branch infrastructure. The one-click compliance reports and real-time threat detection have been transformative for our internal audits. Our ISO 27001 recertification was the smoothest in our history."
"Our university network serves 15,000+ students and hundreds of researchers. After a near-miss ransomware event, we engaged TekkPak to deploy Logsign. Within 48 hours of go-live, it detected 3 compromised faculty devices that traditional antivirus had completely missed. The UEBA module is extraordinary — we've blocked 12 insider threats in 6 months."
"We evaluated Splunk, QRadar, and Logsign extensively. Logsign won on three criteria: unified platform, price point, and TekkPak's local expertise. The deployment was completed in 5 days — compared to the 3-month estimate from Splunk's partner. Logsign's threat intelligence integration has blocked over 4,000 unique malicious IPs targeting our e-commerce platform in the first month alone."
The TekkPak Technologies Advantage
TekkPak isn't just a software reseller. We are a full-cycle cybersecurity implementation partner with deep technical expertise, Pakistan-specific compliance knowledge, and a proven track record of successful Logsign deployments.
Authorized Logsign Reseller
As an officially authorized Logsign reseller in Pakistan, we provide genuine licensed software, official product roadmap access, vendor-backed SLAs, and direct escalation channels to Logsign's global engineering team.
Pakistan-First Expertise
Our engineers understand the unique challenges of Pakistani organizations — SBP regulations, PTA directives, local ISP infrastructure, power considerations for on-premises deployments, and the specific threat actors targeting Pakistani industries.
End-to-End Implementation
From needs assessment and architecture design through deployment, custom rule creation, staff training, and post-go-live support — TekkPak manages every phase. You focus on your business; we ensure your Logsign platform operates at peak performance.
24/7 Managed Support
Cyber threats don't observe business hours. TekkPak offers round-the-clock monitoring support, proactive platform health checks, and rapid incident escalation — ensuring your Logsign environment never has a blind spot.
Knowledge Transfer & Training
We don't just hand over the keys. TekkPak conducts structured, role-based training programs for your SOC analysts, IT administrators, compliance officers, and executive stakeholders — building lasting internal Logsign capability.
Ongoing Use Case Development
The threat landscape evolves constantly. TekkPak's security team continuously develops new Logsign detection rules, playbooks, and dashboards tailored to emerging threats targeting your industry — keeping your defenses always ahead of attackers.
Everything You Need to Know About Logsign in Pakistan
Common questions from IT leaders, CISOs, and procurement teams evaluating Logsign for their organizations.
What is Logsign and how does it differ from a traditional SIEM?
Logsign is a Unified Security Operations Platform (USOP) that combines Next-Generation SIEM (Security Information and Event Management), SOAR (Security Orchestration, Automation, and Response), and User & Entity Behavior Analytics (UEBA) in a single native platform. Unlike traditional SIEM tools that only collect and correlate log data, Logsign also automates the response to detected threats through SOAR playbooks — eliminating the manual work that slows down incident response in legacy security setups.
Why should Pakistani organizations choose Logsign for cybersecurity?
Pakistani organizations face a unique combination of escalating cyber threats, increasing regulatory requirements from the State Bank of Pakistan (SBP) and PTA, and budget constraints that make expensive Western SIEM platforms impractical. Logsign delivers enterprise-grade SIEM and SOAR capabilities at a transparent, cost-effective price point — and when deployed by TekkPak Technologies as the authorized local partner, you benefit from on-ground Pakistani expertise, local compliance knowledge, and rapid deployment timelines that international vendors simply cannot match.
What is the difference between Logsign SIEM and Logsign SOAR?
Logsign SIEM (Security Information and Event Management) is responsible for collecting, normalizing, correlating, and analyzing log data from across your entire infrastructure to detect security threats and generate alerts. Logsign SOAR (Security Orchestration, Automation, and Response) takes those detected threats and automatically executes predefined response actions — such as blocking an IP on your firewall, isolating a compromised endpoint, or creating an incident ticket in your ITSM system. In Logsign's unified platform, these two capabilities work together seamlessly without any integration gaps or additional licensing.
Will Logsign impact my network or application performance?
No. Logsign is built on a distributed big-data architecture that operates entirely out-of-band from your production network. It ingests log data passively without inserting itself into the traffic path. Even at massive log volumes — billions of events per day — Logsign's processing engine operates independently, ensuring zero impact on network latency, application performance, or endpoint resources.
How long does Logsign take to deploy?
With TekkPak Technologies managing the implementation, a standard Logsign deployment is completed within 3–7 business days for most organizations. This includes platform installation, log source onboarding, correlation rule configuration, dashboard setup, and initial playbook automation. Complex enterprise environments with extensive multi-site infrastructure or large numbers of log sources may require 2–4 weeks for a comprehensive deployment — still dramatically faster than competing SIEM platforms that typically take 3–6 months.
Does Logsign support compliance with State Bank of Pakistan (SBP) requirements?
Yes. Logsign includes pre-built compliance content packs that can be mapped to State Bank of Pakistan (SBP) Cybersecurity Framework requirements, including log retention, privileged access monitoring, transaction anomaly detection, and audit trail generation. TekkPak's team has deep familiarity with SBP directives and configures Logsign specifically to support your regulatory reporting obligations — making audit preparation dramatically faster and more reliable.
Can Logsign integrate with our existing firewalls and security tools?
Absolutely. Logsign features 500+ out-of-the-box integrations covering all major firewall vendors (Palo Alto, Fortinet, Check Point, Cisco), endpoint protection platforms (CrowdStrike, Symantec, Microsoft Defender), cloud platforms (AWS, Azure, Google Cloud), ITSM tools (ServiceNow, Jira), threat intelligence feeds, and identity providers (Active Directory, Okta). If you have a less common system, Logsign also supports custom API integrations and CEF/Syslog-based log ingestion — meaning virtually any security tool that generates logs can be connected.
What deployment options does Logsign offer — on-premises or cloud?
Logsign supports flexible deployment models to accommodate your infrastructure and data sovereignty requirements: fully on-premises (hardware or virtual appliance), private cloud, public cloud (AWS, Azure), and hybrid deployments that span multiple environments. For Pakistani organizations with data residency requirements or air-gapped environments, the on-premises deployment model ensures that sensitive log data never leaves your controlled infrastructure. TekkPak will advise on the optimal deployment architecture based on your specific requirements.
Secure Your Organization with Logsign Today
Don't wait for a breach to expose your vulnerabilities. Contact TekkPak Technologies — Pakistan's authorized Logsign implementation partner — for a personalized consultation and live platform demonstration tailored to your industry.
TekkPak Technologies — Authorized Logsign Reseller & Integrator | Serving Pakistan Nationwide
Karachi · Lahore · Islamabad · Faisalabad · Peshawar